Background

I lead the software engineering team for The Boring Company’s Prufrock Tunnel Boring Machine platform. We are a small team who solves huge problems with simple and elegant solutions to realize an ambitious vision.
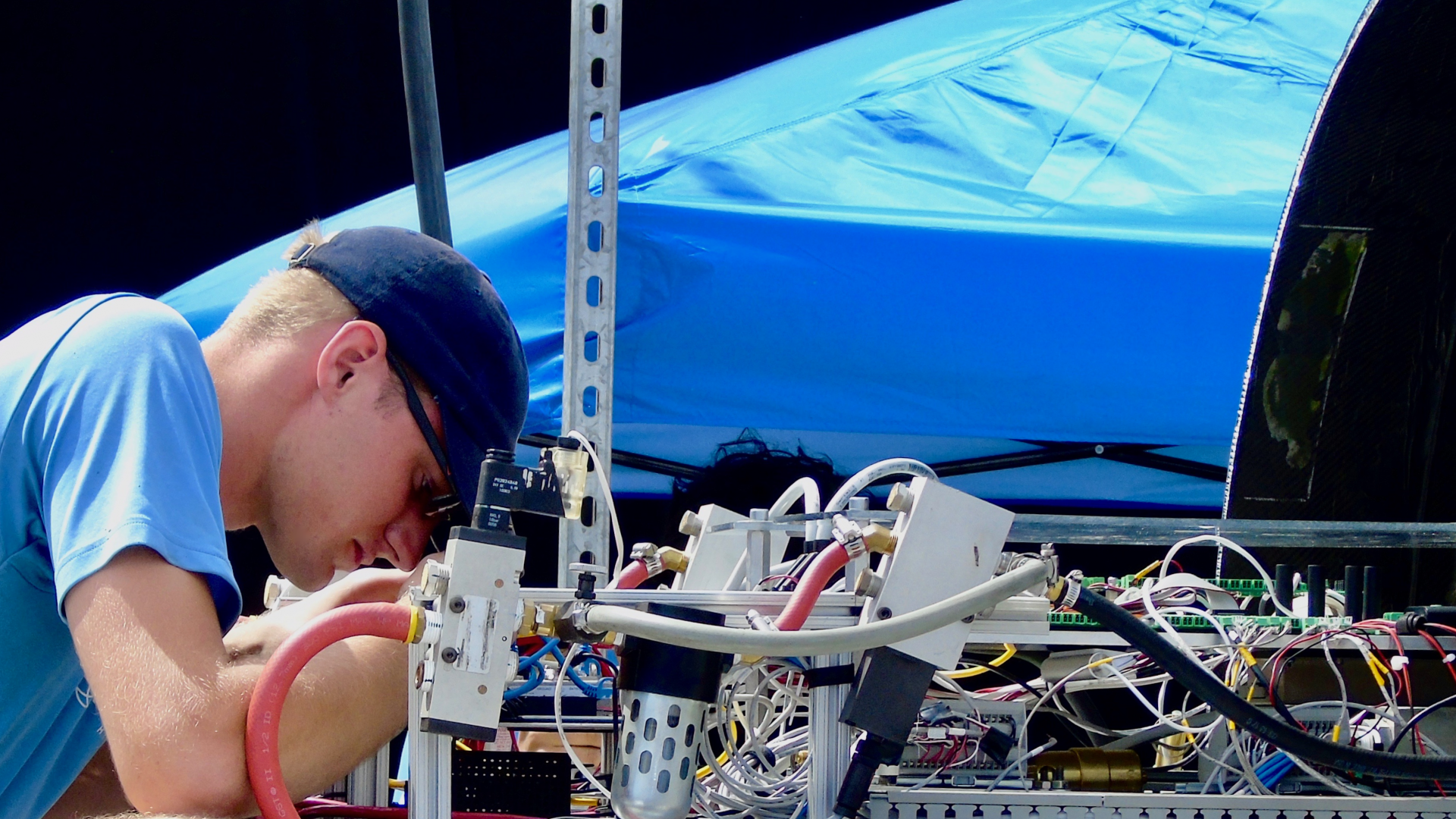
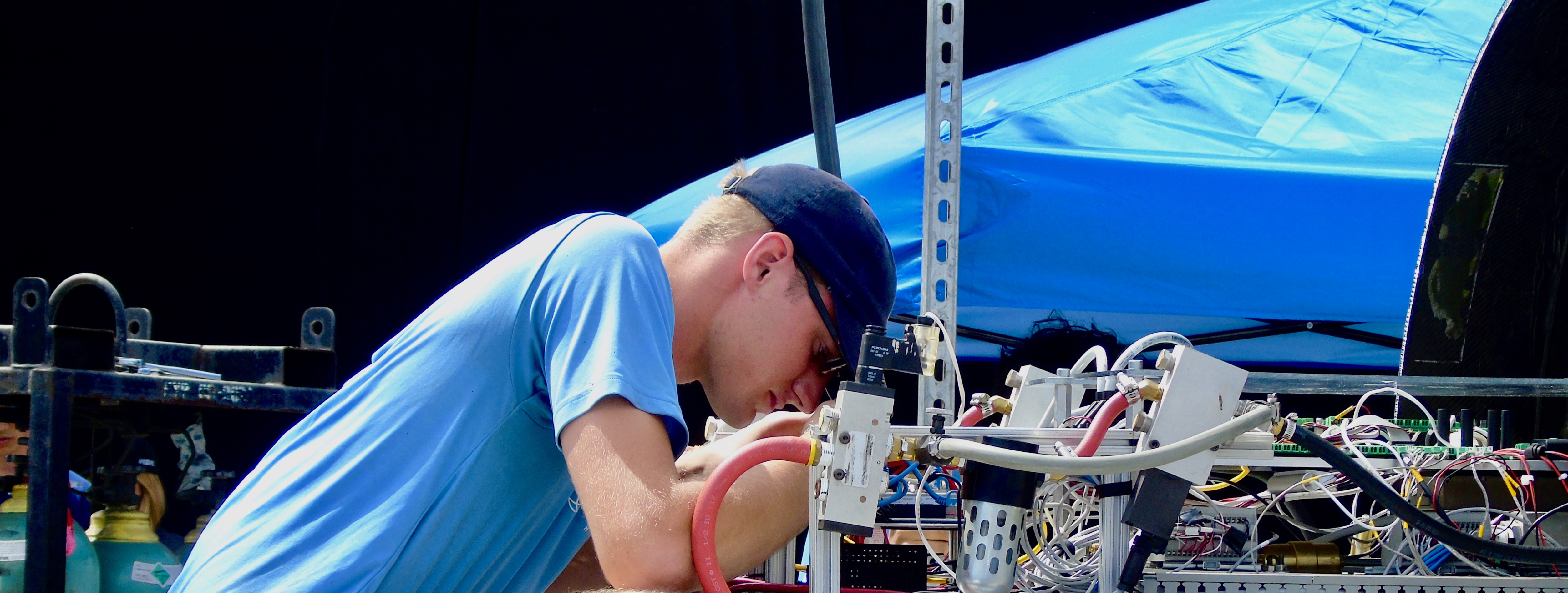
Previously, I worked as a software engineer at Apple and graduated Northeastern University in Boston. I have spent my free time working on cool projects like Elon Musk’s Hyperloop concept and various other self-taught learning experiences.
Over the years I’ve made my way through the stack, starting with front end web development, moving to backend development, Systems Administration, Platform Engineering, Operating Systems, and now Embedded Systems with a focus on industrial automation. I’m always looking to learn something new.
Quick Facts
Who
Experienced software engineer with over 10 years of experience
What
Solves complex problems with simple solutions
When
In software since 2011
Where
Austin, Texas